How to Prove You Can Recover When Prevention Fails
Download the Ransomware Recovery Readiness Checklist to validate your strategy before an attack happens.
Get your copy now

Why Assumed Readiness Isn’t Enough
Most organizations believe they are ready, but few have validated that belief under realistic conditions. Ransomware preparedness is often measured by the tools an organization has deployed, such as endpoint protection and backup software. Yet when ransomware incidents occur, many organizations discover that their readiness was largely assumed rather than tested.
Ransomware exposes gaps between plans and reality. Recovery takes longer than expected, critical data is harder to locate, and dependencies between systems are unclear. Don’t wait until you are making decisions under pressure with incomplete information.
What You Will Discover Inside
This checklist does not prescribe specific tools or architectures.
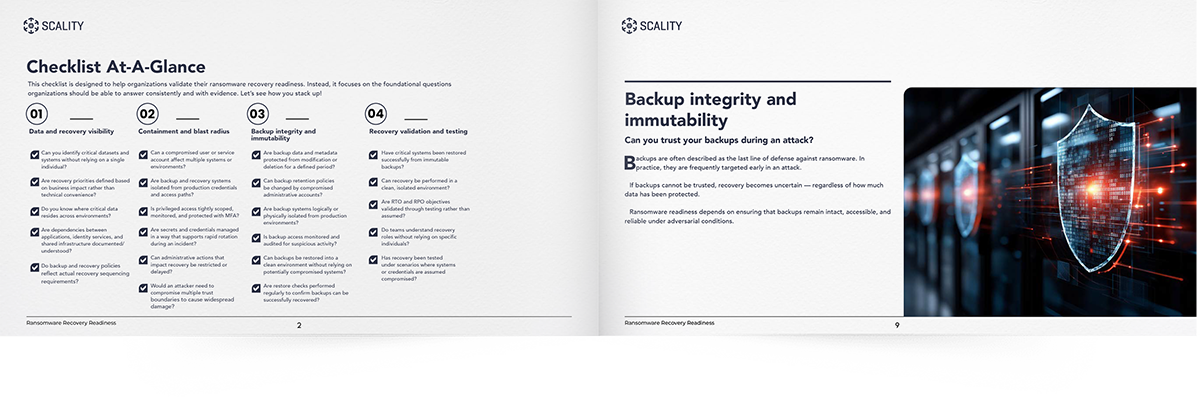
Instead, it focuses on the foundational questions organizations should be able to answer consistently and with evidence across four key pillars:
Achieve Data and Recovery Visibility
Determine if you can identify critical datasets and systems without relying on a single individual. Ensure recovery priorities are defined based on business impact rather than technical convenience.
Limit the Blast Radius
Find out if a compromised user or service account can affect multiple systems or environments. Verify that backup and recovery systems are isolated from production credentials and access paths.
Ensure Backup Integrity and Immutability
Confirm that backup data and metadata are protected from modification or deletion for a defined period. Check if backup retention policies can be changed by compromised administrative accounts.
Validate Your Recovery Strategy
Ask yourself if critical systems have been restored successfully from immutable backups. Understand the importance to validate RTO and RPO objectives through testing rather than assumption.
